Essential Security Measures to Implement Immediately After Linux OS Installation Essential Security Measures to Implement Immediately After Linux OS Installation...
Cybersecurity
How to Prevent Unauthorized Memory Access in Windows Applications: A Comprehensive Security Guide How to Prevent Unauthorized Memory Access in...
How Do Hackers Gain Administrator Access in Under an Hour? How Do Hackers Gain Administrator Access in Under an Hour?...
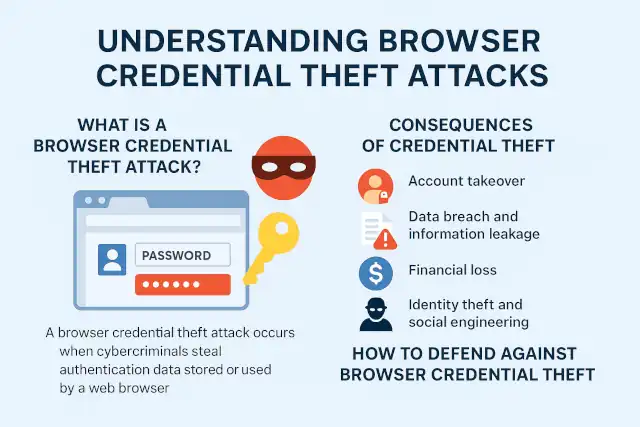
What Is a Browser Credential Theft Attack? What Is a Browser Credential Theft Attack? Understanding Browser Credential Theft Attacks:...
Why VPN Security Should Be Every Enterprise's Top Priority: Lessons from the Mino Kogyo Ransomware Attack Why VPN Security Should...
When and Why You Need Antivirus on Linux (and How to Install ClamAV) When and Why You Need Antivirus on...
Popular Windows 11 Upgrade Tool Flyoobe Targeted by Hackers with Fake Website and Malware Popular Windows 11 Upgrade Tool Flyoobe...
Forget Teamviewer: Build Your Own Relay Server by Open-Source Remote Desktop Forget Teamviewer: Build Your Own Relay Server by Open-Source...
XChat Security Analysis: Safe as "Bitcoin-style" peer-to-peer encryption? XChat Security Analysis: Safe as "Bitcoin-style" peer-to-peer encryption? Elon Musk's announcement of...
Free Encryption Software: A Comprehensive Guide Free Encryption Software: A Comprehensive Guide If you're looking for free encryption software to...
Stronger Encryption Algorithms Beyond AES-256 Stronger Encryption Algorithms Beyond AES-256 AES-256 is widely recognized as a high-strength encryption algorithm, with...
Why MFA Keeps You Safe Even When Passwords Are Compromised Why MFA Keeps You Safe Even When Passwords Are Compromised...
Critical Vulnerabilities Discovered on Oct 26-31: Analysis and Mitigation Strategies Critical Vulnerabilities Discovered on Oct 26-31: Analysis and Mitigation Strategies...
Austria's Military Ditches Microsoft Office: A Neutral Nation's Quest for Digital Sovereignty Austria's Military Ditches Microsoft Office: A Neutral Nation's...
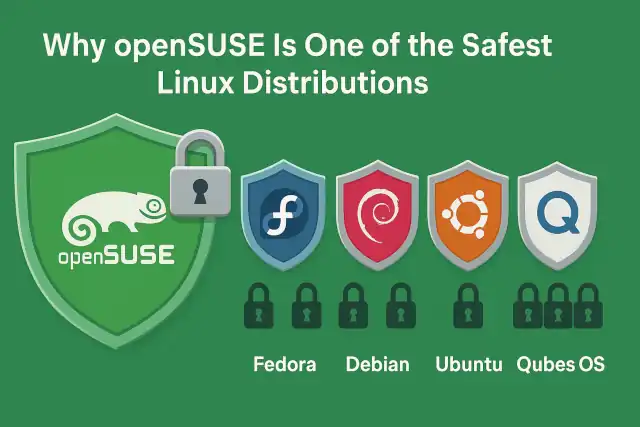
Why openSUSE Is One of the Safest Linux Distributions Why openSUSE Is One of the Safest Linux Distributions When choosing...
TP-Link Routers Face Potential US Ban Over National Security Concerns TP-Link Routers Face Potential US Ban Over National Security Concerns...
Anatomy of a Ransomware Attack: The Askul and Asahi Cyber Incidents In Japan Anatomy of a Ransomware Attack: The Askul...
Why CASB is Essential for Protecting Enterprise Data in Cloud Environments Why CASB is Essential for Protecting Enterprise Data in...
EPP vs EDR: Understanding Critical Endpoint Security Measures EPP vs EDR: Understanding Critical Endpoint Security Measures Introduction In today's increasingly...
How to Prevent Ransomware Infection Risks How to Prevent Ransomware Infection Risks Ransomware has become one of the most dangerous...