Has Your iPhone or Android Phone Been Hacked? Has Your iPhone or Android Phone Been Hacked? Understanding how to determine...
Cybersecurity
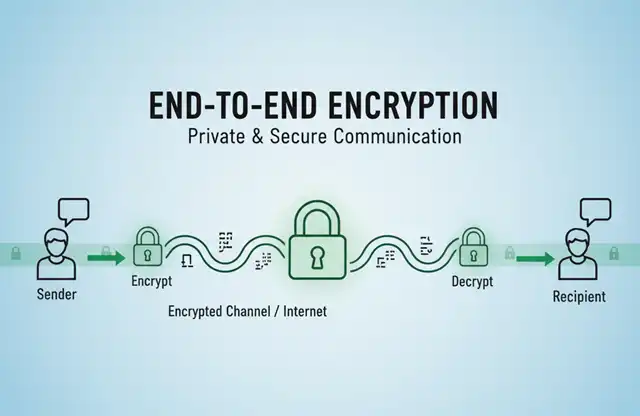
End-to-End Encryption in VoIP: Understanding SIP Protocol and E2EE Support End-to-End Encryption in VoIP: Understanding SIP Protocol and E2EE Support...
The best free email with end-to-end encryption (E2EE) The best free email with end-to-end encryption (E2EE) Here are some of...
Understanding End-to-End Encryption (E2EE): Applications and Use Cases Understanding End-to-End Encryption (E2EE): Applications and Use Cases What is End-to-End Encryption?...
Beyond Passwords: How Passkeys Protect Your Digital Identity Beyond Passwords: How Passkeys Protect Your Digital Identity What Are Passkeys? Understanding...
How to Prevent Mass Email Transmission from Compromised Enterprise Servers? Lessons from the Kumamoto Police Incident How to Prevent Mass...
Linux 6.18 Network Performance Significantly Enhanced: Stronger DDoS Defense and New Hardware Support Linux 6.18 Network Performance Significantly Enhanced: Stronger...
Red Hat's GitLab Repository Breached—Security Investigation Ongoing Red Hat's GitLab Repository Breached—Security Investigation Ongoing In the lifecycle of any enterprise,...
Are Free Cloud Storage Providers Selling Your Data for Profit? Are Free Cloud Storage Providers Selling Your Data for Profit?...
Why Enterprise Firewalls and Antivirus Software Fail to Stop Ransomware Attacks? Why Enterprise Firewalls and Antivirus Software Fail to Stop...
Why Are Enterprises Adopting 3-2-1-1-0 for Data Safety? Why Are Enterprises Adopting 3-2-1-1-0 for Data Safety? The 3-2-1-1-0 Rule: A Modern...
Critical Security Flaw Exposes Windows 11 24H2 Users to Password Theft and Antivirus Bypass Critical Security Flaw Exposes Windows 11...
Qilin Ransomware Group Launches Massive "Korean Leak" Campaign Against Financial Sector Qilin Ransomware Group Launches Massive "Korean Leak" Campaign Against...
OnePlus Acknowledges Critical SMS Vulnerability After Months of Unresponsiveness OnePlus Acknowledges Critical SMS Vulnerability After Months of Unresponsiveness Security researchers...
Steam Removes Malware-Infected Game That Stole $150000 in Cryptocurrency Steam Removes Malware-Infected Game That Stole $150000 in Cryptocurrency. Free game...
Could Quantum Computers Destroy Bitcoin? The Shor's Algorithm Threat Explained. Could Quantum Computers Destroy Bitcoin? The Shor's Algorithm Threat Explained....
Cyberattack Cripples Major European Airports-Forcing Manual Operations Cyberattack Cripples Major European Airports-Forcing Manual Operations Major European airports including London Heathrow,...
Microsoft Edge Patches Critical V8 Zero-Day Vulnerability - Update Recommended Immediately Microsoft Edge Patches Critical V8 Zero-Day Vulnerability - Update...
Is Samsung phone security at risk from its cooperation with Israel? Is Samsung phone security at risk from its cooperation...
Can a Country Remotely Explode Your iPhone? Can a Country Remotely Explode Your iPhone? Executive Summary The question of whether...