Curl 8.4.0 fixes the SOCKS5 heap overflow vulnerability
Curl 8.4.0 is officially released and fixes the SOCKS5 heap overflow vulnerability
- Why Enterprise RAID Rebuilding Succeeds Where Consumer Arrays Fail?
- Linus Torvalds Rejects MMC Subsystem Updates for Linux 7.0: “Complete Garbage”
- The Man Who Maintained Sudo for 30 Years Now Struggles to Fund the Work That Powers Millions of Servers
- How Close Are Quantum Computers to Breaking RSA-2048?
- Why Windows 10 Users Are Flocking to Zorin OS 18 Instead of Linux Mint?
- How to Prevent Ransomware Infection Risks?
- What is the best alternative to Microsoft Office?
Curl 8.4.0 is officially released and fixes the SOCKS5 heap overflow vulnerability. It is recommended to upgrade.
Curl 8.4.0 has been officially released . Founder Daniel Stenberg (community name bagder) has previewed this version a week in advance – fixing high-risk security vulnerabilities, and said that this vulnerability may be the most serious vulnerability encountered by curl in a long time. Affects both the libcurl library and the curl tool.
According to reports, this high-risk vulnerability is a SOCKS5 heap buffer overflow vulnerability ( CVE-2023-38545) that causes curl to overflow the heap-based buffer during the SOCKS5 proxy handshake process .
Some developers explained that the vulnerability occurs when the entered domain name is too long, causing memory overflow . Of course, the prerequisite is that a SOCKS5 proxy is used. Two typical attack scenarios are as follows:
- Some programs have built-in libcurl and allow external users to specify a socket5 proxy and enter an overly long domain name to launch attacks.
- When the user uses curl or libcurl, the socket5 proxy is used, and the http request is sent to the malicious server, and the malicious server returns an http 30x jump, pointing the user’s access target to an over-long domain name, causing overflow.
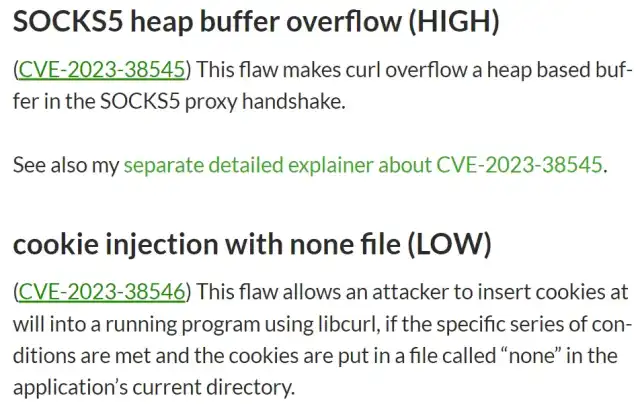
Another vulnerability rated “LOW”, CVE-2023-38546 , is cookie injection via a none file .
This vulnerability allows an attacker to use libcurl to arbitrarily insert a cookie into a running program if a set of specific conditions are met and the cookie is placed in a file named “none” in the application’s current directory.
View details:



