Impossible to be eavesdropped: Huawei Mate 60 Pro Quantum Secure Terminal
Impossible to be eavesdropped: Huawei Mate 60 Pro Quantum Secure Terminal
- Why Enterprise RAID Rebuilding Succeeds Where Consumer Arrays Fail?
- Linus Torvalds Rejects MMC Subsystem Updates for Linux 7.0: “Complete Garbage”
- The Man Who Maintained Sudo for 30 Years Now Struggles to Fund the Work That Powers Millions of Servers
- How Close Are Quantum Computers to Breaking RSA-2048?
- Why Windows 10 Users Are Flocking to Zorin OS 18 Instead of Linux Mint?
- How to Prevent Ransomware Infection Risks?
- What is the best alternative to Microsoft Office?
Impossible to be eavesdropped: Huawei Mate 60 Pro Quantum Secure Terminal
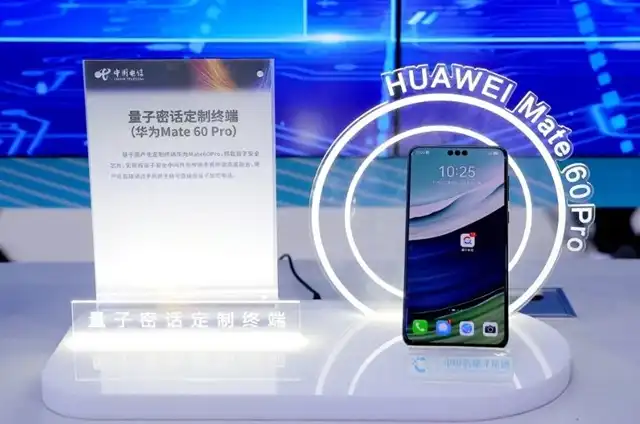
The 2023 Digital Technology Eco Summit in Guangzhou witnessed a showcase of cutting-edge technological advancements by various major tech companies.
At this grand event, in collaboration with China Telecom, Huawei unveiled an eye-catching quantum security product—the Huawei Mate 60 Pro Quantum Secure Terminal, offering users an unprecedented level of communication security.
This terminal ingeniously integrates quantum information technology with VoLTE networks, employing domestically-produced chips, national cryptographic algorithms, and a quantum secure SIM card providing triple-layer protection. Beyond ensuring native VoLTE HD calls, it offers encrypted file transfer, secure instant messaging, and secure collaborative office functions, ensuring comprehensive communication security.
Users can directly make quantum encrypted calls via the phone’s native dialer and access encrypted communication features in pre-installed applications. China Telecom actively invites phone manufacturers for deeper cooperation to jointly develop quantum secure phones based on independently controlled core technology and promote customized application development.
To use China Telecom’s Tianyi Quantum Secure Calls, users need to switch their SIM cards to the quantum secure SIM and activate the corresponding service. Notably, during encrypted calls, Tianyi Quantum Secure Calls do not consume data from the primary package or regular call minutes but only use directed data allocated for these services.
The latest teardown report reveals significant progress in the Huawei Mate 60 Pro’s utilization of domestically-produced components. Compared to the Mate 40 Pro of the same price three years ago, the Mate 60 Pro shows an 18% increase in the value share of Chinese-made parts, reaching 47%. Specifically, the Mate 60 Pro’s total component cost is around 3100 RMB, with components manufactured in China valued at approximately $198, marking a roughly 90% increase compared to the Mate 40 Pro.
The teardown uncovers that the Mate 60 Pro features domestic screens from BOE instead of those from Korean manufacturers, with touch screen components supplied by domestic vendors. This move has significantly contributed to the development of domestically-produced components. Furthermore, Huawei integrates HiSilicon-designed chips manufactured by SMIC, showcasing support for and application of core Chinese technology. These data and details illustrate the remarkable achievements of the Huawei Mate 60 Pro in the application of domestically-produced components, earning praise for China’s independent innovative technology.
Overall, the collaboration between China Telecom and Huawei in launching the Mate 60 Pro Quantum Secure Terminal not only marks an innovative breakthrough in communication security but also achieves remarkable success in the utilization of domestically-produced components, contributing to the rise of Chinese technology.
Why is it impossible to eavesdrop the Quantum Secure Terminal?
Quantum Secure Terminals are designed to leverage the fundamental principles of quantum mechanics to create communication that’s theoretically impossible to eavesdrop on due to a few key factors:
Quantum Key Distribution (QKD):
QKD generates encryption keys using the principles of quantum mechanics.
It relies on the behavior of quantum particles (such as photons) to create a key that’s shared between the sender and receiver.
Any attempt to intercept or measure these particles alters their state, making it detectable by both parties.
This feature ensures the security of the key and alerts the communicating parties to any attempted eavesdropping.
Quantum Entanglement:
Quantum Secure Terminals often utilize the phenomenon of entanglement, where two particles become interconnected in such a way that changes to one particle instantly affect the other, regardless of the distance between them.
This property is used to detect any interference or tampering during the transmission of data, making eavesdropping virtually impossible without being detected.
Uncertainty Principle:
The Uncertainty Principle in quantum mechanics states that certain pairs of properties cannot both be precisely known simultaneously.
This inherent uncertainty introduces unpredictability into the behavior of quantum particles, making it extremely difficult to intercept or measure them without altering their state.
These characteristics create a secure communication channel that, in theory, prevents eavesdropping.
However, while quantum secure communication offers strong security guarantees based on the principles of quantum mechanics, it’s essential to note that real-world implementations may still face practical challenges and vulnerabilities that need to be continually addressed and refined.



