Israel Statement Drives Arabic Nations Toward Huawei Cellphone with HarmonyOS
Israel Statement Drives Arabic Nations Toward Huawei Cellphone with HarmonyOS. Why Huawei Cellphone is Difficult to Compromise?
- Why Enterprise RAID Rebuilding Succeeds Where Consumer Arrays Fail?
- Linus Torvalds Rejects MMC Subsystem Updates for Linux 7.0: “Complete Garbage”
- The Man Who Maintained Sudo for 30 Years Now Struggles to Fund the Work That Powers Millions of Servers
- How Close Are Quantum Computers to Breaking RSA-2048?
- Why Windows 10 Users Are Flocking to Zorin OS 18 Instead of Linux Mint?
- How to Prevent Ransomware Infection Risks?
- What is the best alternative to Microsoft Office?
Israel Statement Drives Arabic Nations Toward Huawei Cellphone with HarmonyOS: Technical Security Analysis
Growing Surveillance Awareness Sparks Alternative Operating System Interest.
Recent revelations about mobile surveillance capabilities have prompted privacy-conscious users across Arabic nations to reconsider their smartphone choices. With increasing documentation of sophisticated tracking technologies and surveillance operations, many are exploring alternatives to mainstream mobile operating systems, with Huawei’s HarmonyOS emerging as a compelling option.
The shift comes amid growing awareness of digital surveillance infrastructure. Reports have documented extensive use of surveillance technologies, including the deployment of Israeli-developed spyware like Pegasus across multiple regions. Additionally, concerns have emerged about embedded surveillance software found in popular smartphone brands distributed across the Middle East and North Africa region.
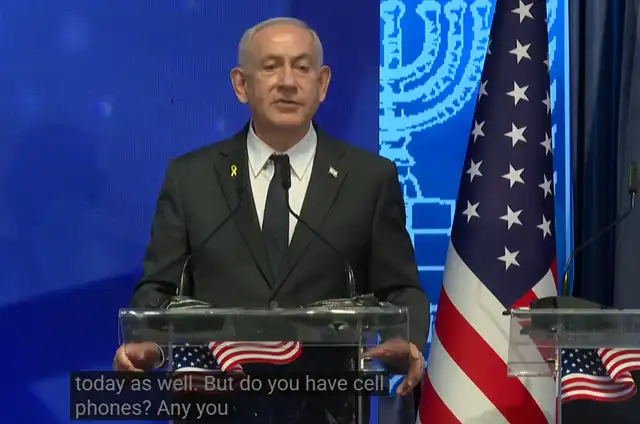
Israel recently publicly stated that if you have a cellphone, Israel knows part of you…
(Snapshot from youtube on Sep 16, 2005)
The HarmonyOS Alternative: Technical Security Architecture
HarmonyOS, particularly the latest HarmonyOS NEXT iteration, presents several technical advantages for privacy-focused users:
1. Closed-Source Kernel Architecture
Unlike Android’s open-source foundation, HarmonyOS NEXT utilizes a closed-source HongMeng kernel. Starting in late 2024, this kernel has been encrypted within the firmware, significantly increasing the difficulty for unauthorized access or reverse engineering by security researchers and potential adversaries.
2. Star Shield Security Framework
The operating system incorporates the “Star Shield” architecture, which provides:
- Stricter Data Permissions: Applications face more restrictive access controls to user data
- Enhanced Encrypted Sharing: Communication between apps and external services uses advanced encryption protocols
- Unauthorized Access Prevention: Built-in tools actively monitor and block suspicious access attempts
3. Hardware-Level Encryption
HarmonyOS NEXT implements individual file encryption using unique keys stored directly on the device’s hardware security module. This approach makes data extraction extremely difficult, even with physical device access.
4. Microkernel Security Certification
The operating system has achieved CC EAL 5+ microkernel security certification, one of the highest levels of security assurance available for commercial operating systems.
Why HarmonyOS is Difficult to Compromise
Technical Barriers to Surveillance
1. Closed Ecosystem Architecture
Unlike Android, which allows extensive third-party modifications and installations, HarmonyOS NEXT operates as a completely closed ecosystem. This eliminates many common attack vectors used by surveillance software.
2. Limited Attack Surface
The operating system restricts unnecessary app permissions by default, reducing the potential entry points for malicious software or surveillance tools.
3. Encrypted Kernel Protection
The encrypted kernel makes it extremely challenging for external parties to:
- Insert surveillance code at the system level
- Monitor system calls and data flow
- Extract encryption keys or sensitive information
4. Independent Software Ecosystem
By completely removing Android app compatibility in HarmonyOS NEXT, Huawei has eliminated the risk of Android-based surveillance tools operating on the platform.
Limitations of Traditional Surveillance Methods
Most commercial surveillance software, including widely documented spyware solutions, relies on:
- Exploiting known vulnerabilities in popular operating systems
- Installing through legitimate app stores using social engineering
- Leveraging system permissions granted to seemingly benign applications
- Accessing standard communication protocols and data storage methods
HarmonyOS NEXT’s architecture specifically addresses these attack vectors through its closed-source design and restricted app ecosystem.
Geopolitical Implications
The potential migration to HarmonyOS in Arabic nations represents more than just a technology shift—it reflects growing concerns about digital sovereignty and privacy protection. Users are increasingly aware that mobile devices can serve as surveillance tools, collecting location data, communications, and personal information.
The closed nature of HarmonyOS, while limiting for researchers and developers, provides a significant advantage for users seeking to avoid surveillance. The difficulty in analyzing or modifying the system works both ways—if security researchers cannot easily examine it, neither can those seeking to exploit it for surveillance purposes.
Challenges and Considerations
App Ecosystem Limitations
The primary challenge facing HarmonyOS adoption is its limited app ecosystem. Users must rely on Huawei’s AppGallery and compatible applications, which may not include all desired software options.
Update and Support Concerns
Long-term security depends on consistent updates and patches. Users must weigh the benefits of a closed, harder-to-penetrate system against the transparency typically required for independent security auditing.
Hardware Dependency
HarmonyOS benefits are maximized on Huawei hardware, which may not be available or desirable in all markets due to various trade restrictions.
Conclusion
As awareness of mobile surveillance capabilities continues to grow, HarmonyOS presents a technically viable alternative for privacy-conscious users. Its closed-source architecture, encrypted kernel, and restricted ecosystem create significant barriers to unauthorized access and surveillance.
However, the decision to adopt HarmonyOS involves trade-offs between enhanced privacy protection and ecosystem limitations. For users in Arabic nations prioritizing privacy over app selection, HarmonyOS NEXT offers compelling technical advantages that make surveillance significantly more challenging compared to traditional mobile operating systems.
The shift toward alternative operating systems reflects a broader trend of users taking active steps to protect their digital privacy in an increasingly connected world. As these technologies continue to evolve, the balance between security, privacy, and functionality will remain a critical consideration for smartphone users globally.
What is CC EAL 5+ Microkernel Security Certification?
CC EAL 5+ refers to a high-level security certification under the Common Criteria (CC, ISO/IEC 15408) international standard, often applied to operating system kernels—especially microkernels.
Systems such as Huawei’s HarmonyOS microkernel or SYSGO’s PikeOS have highlighted this certification.
1. What are CC and EAL?
-
CC (Common Criteria): An internationally recognized information security evaluation standard (ISO/IEC 15408) used to assess IT products and systems.
-
EAL (Evaluation Assurance Level): Security assurance levels range from EAL1 to EAL7. The higher the number, the stricter and more comprehensive the evaluation.
2. What does EAL 5 and the “+” mean?
-
EAL5: Indicates that the system’s security design and implementation have undergone rigorous formal and semi-formal verification methods, not just functional testing. It ensures strong security assurance while maintaining practical usability.
-
“+”: Means additional enhanced testing or verification beyond the standard EAL5 requirements, often strengthening key security mechanisms such as access control, cryptography, memory isolation, and attack resistance.
In short, EAL 5+ is considered a high-level security certification, bridging advanced commercial and certain military-grade requirements.
3. Why “microkernel”?
Microkernel architecture is well-suited for high-assurance security because:
-
It is minimal, containing only the most essential functions (e.g., memory management, process scheduling, inter-process communication).
-
Other components (drivers, file systems, networking) run in user space.
-
This separation makes it easier to contain failures or attacks, while the core remains secure and stable.
-
The minimal core is also more feasible for formal verification.
4. Application Areas
Systems certified at CC EAL 5+ with a microkernel architecture are typically used in:
-
Telecom-grade operating systems (e.g., 5G networks)
-
Financial and payment systems
-
Aerospace and railway control
-
Government, defense, and critical infrastructure security
In short:
CC EAL 5+ microkernel security certification means that a microkernel-based operating system has passed the Common Criteria’s EAL5 with enhanced assurance (“+”) level, demonstrating high reliability and strong resistance to attacks, making it suitable for mission-critical and high-security environments.



