Researchers Uncover New Method for Stealing SSH Encryption Keys
Researchers Uncover New Method for Stealing SSH Encryption Keys
- Why Enterprise RAID Rebuilding Succeeds Where Consumer Arrays Fail?
- Linus Torvalds Rejects MMC Subsystem Updates for Linux 7.0: “Complete Garbage”
- The Man Who Maintained Sudo for 30 Years Now Struggles to Fund the Work That Powers Millions of Servers
- How Close Are Quantum Computers to Breaking RSA-2048?
- Why Windows 10 Users Are Flocking to Zorin OS 18 Instead of Linux Mint?
- How to Prevent Ransomware Infection Risks?
- What is the best alternative to Microsoft Office?
Researchers Uncover New Method for Stealing SSH Encryption Keys
Security researchers have devised a new method to pilfer encryption keys in SSH (Secure Shell) communication between computers and servers.
Compromised SSH connections can enable malicious actors to monitor or infiltrate data exchanged between enterprise servers and remote clients.
This research builds upon a foundation of the past 25 years of studies.
The vulnerability exploits minor computational errors that naturally occur during the SSH handshake process. Fortunately, it is only applicable to RSA encryption. Unfortunately, the RSA algorithm accounts for approximately one-third of the tested websites. Among around 3.5 billion public website signatures scanned over the past seven years, about one billion use RSA. Within this subset, approximately one million implementations expose their SSH keys.
“In our data, approximately one in a million SSH signatures exposes the private key of the SSH host,” co-author Keegan Ryan stated. “While this scenario is rare, the vast traffic on the internet means that these RSA failures in SSH occur frequently.”
Worse still, hackers could exploit the same or similar techniques to compromise IPsec connections. In their recent paper titled “Passive SSH Key Compromise via Lattice Attacks,” researchers point out that this could spell disaster for companies or individuals using VPNs to ensure secure connections and hide internet traffic: “In this paper, we demonstrate passive RSA key compromise from a single erroneous signature added by PKCS#1 v1.5 in both SSH and IPsec protocols using lattice attacks as described by Coron et al.”
Traditional exploiters intentionally disrupt the process, causing errors in the handshake. Alternatively, attackers can passively wait for errors to occur. After capturing the erroneous signature, they use “greatest common divisor” operations to compare it with a valid signature, obtaining one of the prime numbers that ensures key security. However, this new attack utilizes a branch of grid-based cryptography.
Once the attacker gains access to the key, they can launch a man-in-the-middle attack. The server controlled by the hacker uses the ill-gotten key to impersonate the attacked server, intercepting and responding to incoming SSH communication. This makes it easy to steal credentials and other information. If the attacker obtains an incorrect key, the same scenario occurs with IPsec communication.
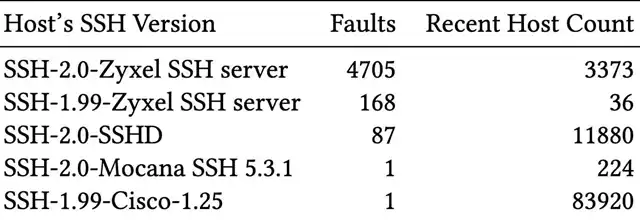
The vulnerability was primarily found in devices from four manufacturers (Cisco, Zyxel, Hillstone Networks, and Mocana). Researchers notified the original equipment manufacturers before disclosing the vulnerability. Only Cisco and Zyxel responded promptly, while Hillstone responded after the publication.
The latest mitigations for Transport Layer Security strengthen defenses against such attacks. Ryan emphasized that other security protocols must adopt similar measures, especially SSH and IPsec, given their widespread use. Nevertheless, the individual risk of such hacker attacks remains relatively low.
You can read or download all technical details from the cryptographic ePrint archive website:



