Critical Alert: Fake 7-Zip Website Distributes Malware, Turns PCs Into Proxy Botnets Critical Alert: Fake 7-Zip Website Distributes Malware, Turns...
Cybersecurity
Windows 11 Introduces Major Security Overhaul: Smartphone-Style Permissions Coming to Desktop Windows 11 Introduces Major Security Overhaul: Smartphone-Style Permissions Coming...
Critical Windows Notepad Vulnerability Patched: What Users Need to Know Critical Windows Notepad Vulnerability Patched: What Users Need to Know...
Microsoft Warns of Sophisticated New Malware Campaign Targeting Enterprise Users Microsoft Warns of Sophisticated New Malware Campaign Targeting Enterprise Users....
The 11-Year Security Nightmare: How CVE-2026-24061 Left Your NAS Wide Open The 11-Year Security Nightmare: How CVE-2026-24061 Left Your NAS...
Notepad++ Infrastructure Hijacked: A Six-Month Global Supply Chain Campaign Notepad++ Infrastructure Hijacked: A Six-Month Global Supply Chain Campaign The popular...
Android 16: Thieves Can't Access Your Apps Even If They Steal Your Password Android 16: Thieves Can't Access Your Apps...
Why Google Took Down IPIDEA: Understanding the Hidden Dangers of Residential Proxy Networks Why Google Took Down IPIDEA: Understanding the...
NVIDIA Issues Critical Security Update for GPU Drivers: Users Urged to Update Immediately NVIDIA Issues Critical Security Update for GPU...
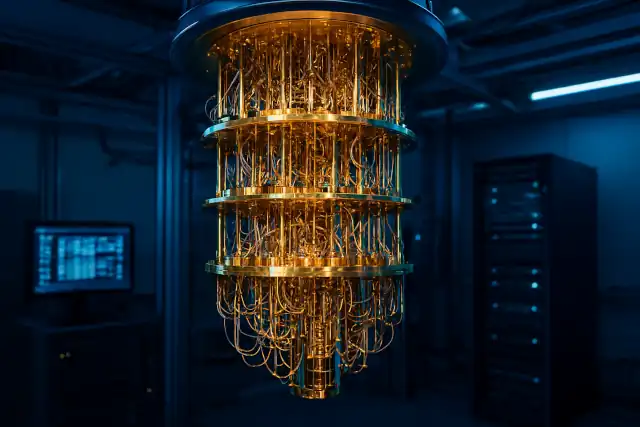
US Government Accelerates Post-Quantum Cryptography Transition as Quantum Threats Loom Closer US Government Accelerates Post-Quantum Cryptography Transition as Quantum Threats...
Critical WinRAR Vulnerability Actively Exploited: Google Urges Immediate Update Critical WinRAR Vulnerability Actively Exploited: Google Urges Immediate Update Global security...
Security Alert: Critical Vulnerability Found in Popular Router Models Security Alert: Critical Vulnerability Found in Popular Router Models A high-severity...
What are Disk Encryption Alternatives If You Think BitLocker Unsafe? What are Disk Encryption Alternatives If You Think BitLocker Unsafe?...
Why "Never Use Public Wi-Fi" and Other Common Advice May Be Outdated? Why "Never Use Public Wi-Fi" and Other Common...
Hidden Threat: Cryptomining Malware Embedded in Free Gaming Software Hidden Threat: Cryptomining Malware Embedded in Free Gaming Software Growing Concern...
Linux Security: Why "Install What You Can Audit" Remains the Core Defense Against Malware Linux Security: Why "Install What You...
The Rise of "Vibescamming": When AI Becomes a Cybercriminal's Best Tool The Rise of "Vibescamming": When AI Becomes a Cybercriminal's...
Is Your Website Really Safe Just Because You Installed an SSL Certificate? Is Your Website Really Safe Just Because You...
Let's Encrypt to Launch Free IP Address Certificates: A Game-Changer for DevOps and IoT Let's Encrypt to Launch Free IP...
Critical Zero-Day Vulnerability Affects Apple Devices: Urgent Update Required Critical Zero-Day Vulnerability Affects Apple Devices: Urgent Update Required Apple has...