Proton Launches Encrypted Spreadsheet Tool to Challenge Tech Giants on Privacy Proton Launches Encrypted Spreadsheet Tool to Challenge Tech Giants...
Cybersecurity
What are Free SSL Certificate Alternatives to Let's Encrypt? What are Free SSL Certificate Alternatives to Let's Encrypt? As Let's...
Why Smartphone Chat Apps Are Not Safe Enough? Why Smartphone Chat Apps Are Not Safe Enough: Understanding the Security Gaps...
Will Quantum Computers Break All Our Passwords in 20 Years? Will Quantum Computers Break All Our Passwords in 20 Years?...
Can Website Security Certificates Be Forged? A Technical Analysis Can Website Security Certificates Be Forged? A Technical Analysis The Vulnerability...
How HTTPS Protocol Shields Your Private Data from Prying Eyes? How HTTPS Protocol Shields Your Private Data from Prying Eyes?...
Telegram Founder Launches Cocoon: A Decentralized Network Challenging Big Tech's AI Monopoly Telegram Founder Launches Cocoon: A Decentralized Network Challenging...
Google Releases December 2025 Android Security Update: Multiple Critical Vulnerabilities Patched, Evidence of Active Exploitation Google Releases December 2025 Android...
Why Endpoint Protection Platforms Are Superior to Traditional Antivirus? Why Endpoint Protection Platforms Are Superior to Traditional Antivirus? In today's...
Thailand Orders Worldcoin to Delete Over 1.2 Million Iris Scans and Halt Operations Thailand Orders Worldcoin to Delete Over 1.2...
OpenAI Discloses Potential User Data Breach Through Third-Party Analytics Provider OpenAI Discloses Potential User Data Breach Through Third-Party Analytics Provider...
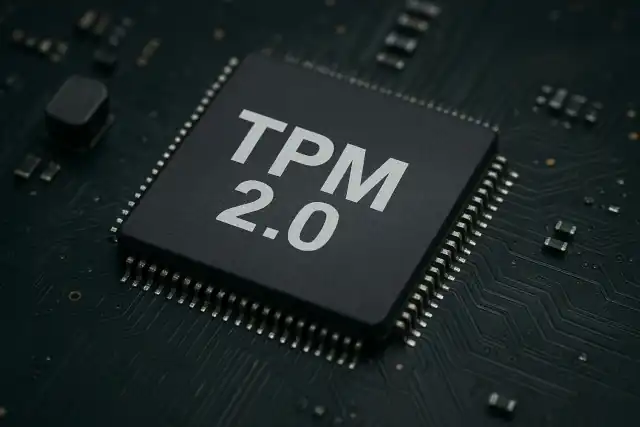
Will Linux Adopt TPM 2.0 Mandatory Like Windows 11 near soon? Understanding the Future of PC Security Will Linux Adopt...
Why Can't Criminals "Ghost Tap" Your iPhone or Android Wallet? Why Can't Criminals "Ghost Tap" Your iPhone or Android Wallet?...
"123456" and "Password" Still Reign: Most Dangerous Login Habits Exposed "123456" and "Password" Still Reign: Most Dangerous Login Habits Exposed...
Why Xubuntu Migrated from WordPress to Hugo: A Security Wake-Up Call Why Xubuntu Migrated from WordPress to Hugo: A Security...
How Helios Encryption Works: When Top-Tier Security Meets Human Error How Helios Encryption Works: When Top-Tier Security Meets Human Error...
Lessons from the Jaguar Land Rover Ransomware Attack: When Human Trust Becomes the Weakest Link Lessons from the Jaguar Land...
The IoT Time Bomb: Lessons from Microsoft's Battle with Aisuru's Botnet The IoT Time Bomb: Lessons from Microsoft's Battle with...
World's First Self-Destructing SSD: T-CREATE EXPERT P35S Enables One-Button Data Destruction World's First Self-Destructing SSD: T-CREATE EXPERT P35S Enables One-Button...
Why You Need DNS over HTTPS or DNS over TLS to Protect Your Privacy? Why You Need DNS over HTTPS...