Microsoft Releases December 2025 Windows Update: Addresses Critical Office Vulnerabilities Microsoft Releases December 2025 Windows Update: Addresses Critical Office Vulnerabilities...
Hacker
Can Passwords Still Be Transmitted in Plain Text with HTTPS? Can Passwords Still Be Transmitted in Plain Text with HTTPS?...
Telegram Tests Passkey Login: No Phone Number or Verification Code Required Telegram Tests Passkey Login: No Phone Number or Verification...
Why DMARC Is Crucial for Preventing Email Spoofing and Phishing Attacks? Why DMARC Is Crucial for Preventing Email Spoofing and...
Why Passkeys Will Replace Passwords: The Future of Digital Authentication Why Passkeys Will Replace Passwords: The Future of Digital Authentication...
What Are Decentralized End-to-End Encrypted Messaging Apps and Why Do They Matter? What Are Decentralized End-to-End Encrypted Messaging Apps and...
Is the One-Time Pad Truly Unbreakable? Understanding Cryptography's Perfect Cipher Is the One-Time Pad Truly Unbreakable? Understanding Cryptography's Perfect Cipher...
Microsoft Quietly Patches Long-Standing Windows Shortcut Vulnerability After Years of Refusal Microsoft Quietly Patches Long-Standing Windows Shortcut Vulnerability After Years...
Beware of Poisoned Pirated Movies: DCRat Backdoor Hidden Using Go Compiler Beware of Poisoned Pirated Movies: DCRat Backdoor Hidden Using...
Proton Launches Encrypted Spreadsheet Tool to Challenge Tech Giants on Privacy Proton Launches Encrypted Spreadsheet Tool to Challenge Tech Giants...
What are Free SSL Certificate Alternatives to Let's Encrypt? What are Free SSL Certificate Alternatives to Let's Encrypt? As Let's...
Why Smartphone Chat Apps Are Not Safe Enough? Why Smartphone Chat Apps Are Not Safe Enough: Understanding the Security Gaps...
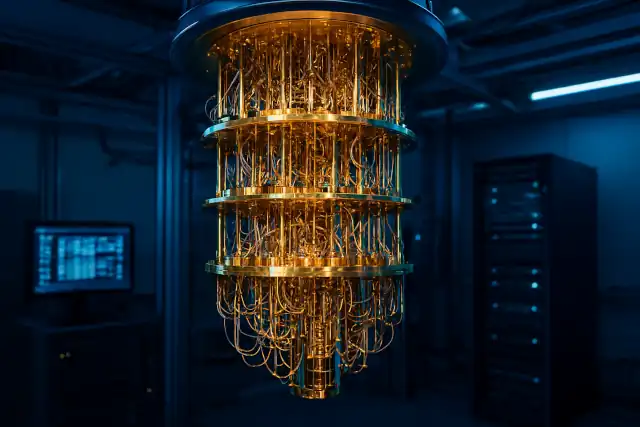
Will Quantum Computers Break All Our Passwords in 20 Years? Will Quantum Computers Break All Our Passwords in 20 Years?...
Can Website Security Certificates Be Forged? A Technical Analysis Can Website Security Certificates Be Forged? A Technical Analysis The Vulnerability...
How HTTPS Protocol Shields Your Private Data from Prying Eyes? How HTTPS Protocol Shields Your Private Data from Prying Eyes?...
Why Endpoint Protection Platforms Are Superior to Traditional Antivirus? Why Endpoint Protection Platforms Are Superior to Traditional Antivirus? In today's...
Thailand Orders Worldcoin to Delete Over 1.2 Million Iris Scans and Halt Operations Thailand Orders Worldcoin to Delete Over 1.2...
OpenAI Discloses Potential User Data Breach Through Third-Party Analytics Provider OpenAI Discloses Potential User Data Breach Through Third-Party Analytics Provider...
Why Can't Criminals "Ghost Tap" Your iPhone or Android Wallet? Why Can't Criminals "Ghost Tap" Your iPhone or Android Wallet?...
"123456" and "Password" Still Reign: Most Dangerous Login Habits Exposed "123456" and "Password" Still Reign: Most Dangerous Login Habits Exposed...