How Did Tesla and Major Companies Fall Victim to Cryptojacking? How Did Tesla and Major Companies Fall Victim to Cryptojacking?...
Hacker
How to Prevent SSH Brute Force Attacks: A Comprehensive Guide How to Prevent SSH Brute Force Attacks: A Comprehensive Guide...
How to Defend Against Large-Scale DDoS Attacks: A Comprehensive Strategy How to Defend Against Large-Scale DDoS Attacks: A Comprehensive Strategy...
Why Enterprises Must Implement Zero Trust Security? Why Enterprises Must Implement Zero Trust Security? Introduction In an era where cyber...
Essential Security Measures to Implement Immediately After Linux OS Installation Essential Security Measures to Implement Immediately After Linux OS Installation...
How to Prevent Unauthorized Memory Access in Windows Applications: A Comprehensive Security Guide How to Prevent Unauthorized Memory Access in...
How Do Hackers Gain Administrator Access in Under an Hour? How Do Hackers Gain Administrator Access in Under an Hour?...
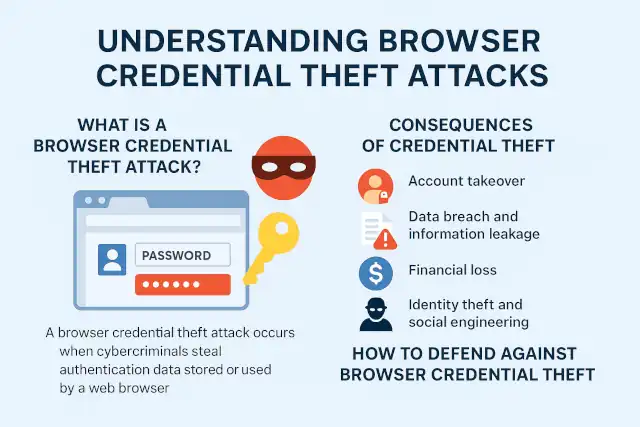
What Is a Browser Credential Theft Attack? What Is a Browser Credential Theft Attack? Understanding Browser Credential Theft Attacks:...
How China's Financial Controls Are Winning the Ransomware War How China's Financial Controls Are Winning the Ransomware War? Ransomware remains...
Qilin Ransomware Group Launches Massive "Korean Leak" Campaign Against Financial Sector Qilin Ransomware Group Launches Massive "Korean Leak" Campaign Against...
Hackers threaten to leak 80GB of confidential data stolen from Reddit Hackers threaten to leak 80GB of confidential data...