The Fall of Fax Security: Why VoIP Killed the "Secure" Transmission? The Fall of Fax Security: Why VoIP Killed the...
Networking
Which Honeypot Is Best for Enterprise Security Teams? Which Honeypot Is Best for Enterprise Security Teams? Introduction Honeypots have become...
FIN7 Hackers Exploit Windows SSH Backdoors for Covert Remote Access and Persistence FIN7 Hackers Exploit Windows SSH Backdoors for Covert...
How Did Tesla and Major Companies Fall Victim to Cryptojacking? How Did Tesla and Major Companies Fall Victim to Cryptojacking?...
How to Prevent SSH Brute Force Attacks: A Comprehensive Guide How to Prevent SSH Brute Force Attacks: A Comprehensive Guide...
How to Defend Against Large-Scale DDoS Attacks: A Comprehensive Strategy How to Defend Against Large-Scale DDoS Attacks: A Comprehensive Strategy...
Why Enterprises Must Implement Zero Trust Security? Why Enterprises Must Implement Zero Trust Security? Introduction In an era where cyber...
How Do Hackers Gain Administrator Access in Under an Hour? How Do Hackers Gain Administrator Access in Under an Hour?...
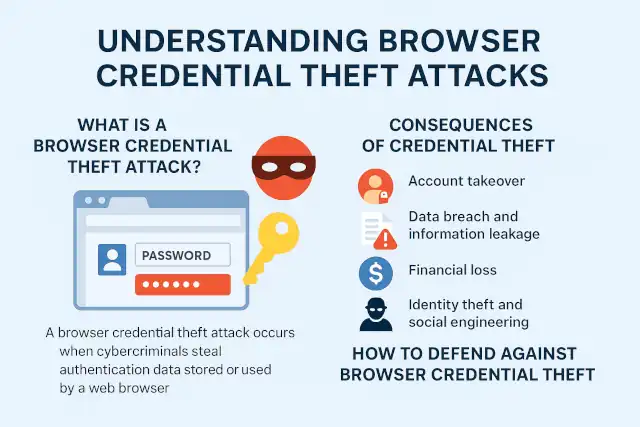
What Is a Browser Credential Theft Attack? What Is a Browser Credential Theft Attack? Understanding Browser Credential Theft Attacks:...
Why VPN Security Should Be Every Enterprise's Top Priority: Lessons from the Mino Kogyo Ransomware Attack Why VPN Security Should...
Popular Windows 11 Upgrade Tool Flyoobe Targeted by Hackers with Fake Website and Malware Popular Windows 11 Upgrade Tool Flyoobe...
Forget Teamviewer: Build Your Own Relay Server by Open-Source Remote Desktop Forget Teamviewer: Build Your Own Relay Server by Open-Source...
XChat Security Analysis: Safe as "Bitcoin-style" peer-to-peer encryption? XChat Security Analysis: Safe as "Bitcoin-style" peer-to-peer encryption? Elon Musk's announcement of...
Why MFA Keeps You Safe Even When Passwords Are Compromised Why MFA Keeps You Safe Even When Passwords Are Compromised...
Critical Vulnerabilities Discovered on Oct 26-31: Analysis and Mitigation Strategies Critical Vulnerabilities Discovered on Oct 26-31: Analysis and Mitigation Strategies...
TP-Link Routers Face Potential US Ban Over National Security Concerns TP-Link Routers Face Potential US Ban Over National Security Concerns...
Anatomy of a Ransomware Attack: The Askul and Asahi Cyber Incidents In Japan Anatomy of a Ransomware Attack: The Askul...
Why CASB is Essential for Protecting Enterprise Data in Cloud Environments Why CASB is Essential for Protecting Enterprise Data in...
EPP vs EDR: Understanding Critical Endpoint Security Measures EPP vs EDR: Understanding Critical Endpoint Security Measures Introduction In today's increasingly...
TrueNAS 25.10 "Goldeye" Released with NVMe-oF Support and Major Virtualization Upgrades TrueNAS 25.10 "Goldeye" Released with NVMe-oF Support and Major...