How to Prevent Ransomware Infection Risks How to Prevent Ransomware Infection Risks Ransomware has become one of the most dangerous...
Networking
How Can pfSense Protect Your Network Against DDoS Attacks? How Can pfSense Protect Your Network Against DDoS Attacks? Deploying pfSense...
Critical Security Vulnerabilities Discovered in TP-Link Omada Gateway Products Critical Security Vulnerabilities Discovered in TP-Link Omada Gateway Products October 28,...
How China's Financial Controls Are Winning the Ransomware War How China's Financial Controls Are Winning the Ransomware War? Ransomware remains...
Why Satellite Companies Haven’t Encrypted Most Communications Why Satellite Companies Haven’t Encrypted Most Communications? A groundbreaking study, awarded the Distinguished...
UEFI Security: Can Firmware Be Infected by Malware? UEFI Security: Can Firmware Be Infected by Malware? Introduction UEFI (Unified Extensible...
High-Performance Gaming Mice Could Be Turned Into Surveillance Tools High-Performance Gaming Mice Could Be Turned Into Surveillance Tools, UC Research...
Why Pritunl Outshines OpenVPN and WireGuard: A Comprehensive Guide Why Pritunl Outshines OpenVPN and WireGuard: A Comprehensive Guide Introduction When...
How Online Stores Can Protect Themselves from Ransomware Attacks How Online Stores Can Protect Themselves from Ransomware Attacks A Wake-Up...
Microsoft Patches "Highest-Ever Rated" ASP.NET Core Vulnerability Microsoft Patches "Highest-Ever Rated" ASP.NET Core Vulnerability REDMOND, WA - October 19, 2025...
Why Linux Doesn't Need Antivirus Software (But Windows Does) Why Linux Doesn't Need Antivirus Software (But Windows Does) The debate...
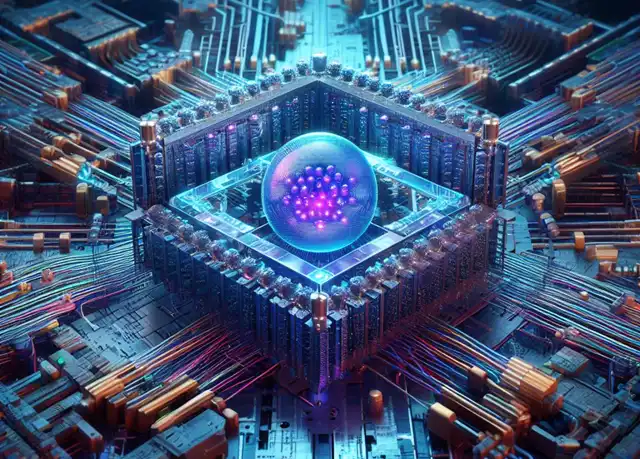
Quantum Computers Will Break Today's Encryption And Hackers Are Already Preparing Quantum Computers Will Break Today's Encryption And Hackers Are...
Why PQC Encryption Technology Can Resist Quantum Computing Decryption Why PQC Encryption Technology Can Resist Quantum Computing Decryption ASUSTOR NAS...
Why Browser Password Managers Deserve More Credit Than They Get Why Browser Password Managers Deserve More Credit Than They Get...
Japan's Long-Delayed Shift to "True 5G" Finally Gains Momentum Japan's Long-Delayed Shift to "True 5G" Finally Gains Momentum. Why the...
US Seizes Record $15 Billion in Bitcoin: Charges 'Prince Group' Chairman Over Forced Labor Scam US Seizes Record $15 Billion...
Ransomware Attackers Prioritize Data Theft Over Encryption as Attacks Become Multi-Dimensional Ransomware Attackers Prioritize Data Theft Over Encryption as Attacks...
Samsung Announces HBM4e Memory for 2027: Bandwidth to Reach 3.25TB/s Samsung Announces HBM4e Memory for 2027: Bandwidth to Reach 3.25TB/s....
TP-Link Successfully Completes First Wi-Fi 8 Hardware Trial: A Leap Forward in Wireless Reliability TP-Link Successfully Completes First Wi-Fi 8...
What is the Soft-routing (Soft Router)? What is Soft-Routing (Soft Router)? Soft routing, commonly called a "soft router," represents a...