Critical 13-Year-Old Redis Lua Vulnerability Enables Remote Code Execution Critical 13-Year-Old Redis Lua Vulnerability Enables Remote Code Execution Redis has...
Networking
RustDesk vs TeamViewer: A Security-Focused Comparison RustDesk vs TeamViewer: A Security-Focused Comparison Remote desktop software has become essential for IT...
CAT5e CAT6 CAT6a CAT7 Comparison CAT5e CAT6 CAT6a CAT7 Comparison CAT5e, CAT6, CAT6a, and CAT7: A Comparison The primary differences...
Can Google see the password saved in Chrome Password Manager? Can Google see the password saved in Chrome Password Manager?...
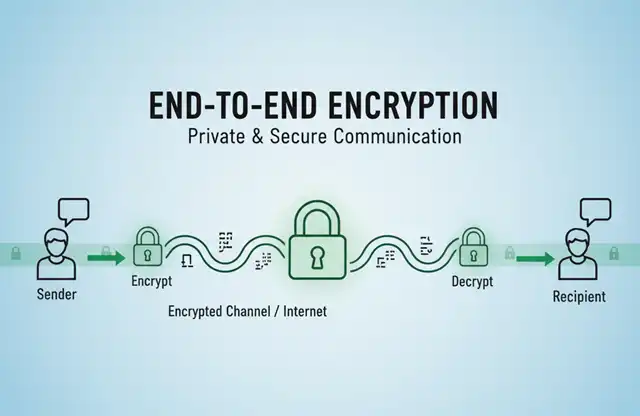
The best free email with end-to-end encryption (E2EE) The best free email with end-to-end encryption (E2EE) Here are some of...
Understanding End-to-End Encryption (E2EE): Applications and Use Cases Understanding End-to-End Encryption (E2EE): Applications and Use Cases What is End-to-End Encryption?...
Beyond Passwords: How Passkeys Protect Your Digital Identity Beyond Passwords: How Passkeys Protect Your Digital Identity What Are Passkeys? Understanding...
How to Prevent Mass Email Transmission from Compromised Enterprise Servers? Lessons from the Kumamoto Police Incident How to Prevent Mass...
T-Mobile to Begin Phasing Out 4G LTE Network: Reallocating Spectrum for 5G Expansion T-Mobile to Begin Phasing Out 4G LTE...
Beyond 5G: How Terahertz Waves Will Power the Next Generation of 6G Wireless Networks Beyond 5G: How Terahertz Waves Will...
Why Moon Wi-Fi Is So Extraordinarily Difficult? Why Moon Wi-Fi Is So Extraordinarily Difficult? NASA Funds Development of Moon Wi-Fi...
Red Hat's GitLab Repository Breached—Security Investigation Ongoing Red Hat's GitLab Repository Breached—Security Investigation Ongoing In the lifecycle of any enterprise,...
Why Enterprise Firewalls and Antivirus Software Fail to Stop Ransomware Attacks? Why Enterprise Firewalls and Antivirus Software Fail to Stop...
Critical Security Flaw Exposes Windows 11 24H2 Users to Password Theft and Antivirus Bypass Critical Security Flaw Exposes Windows 11...
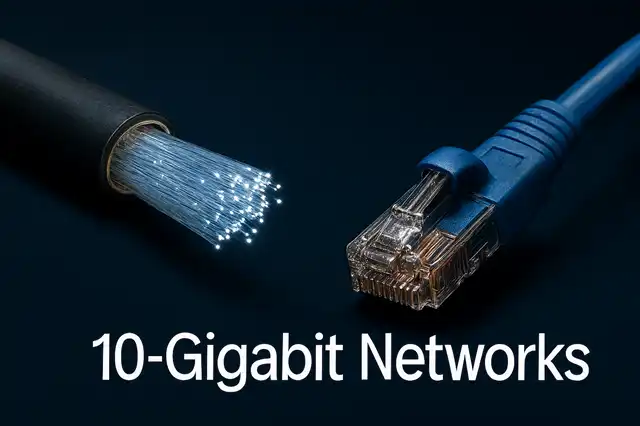
When Will 10-Gigabit Networks Become Mainstream? When Will 10-Gigabit Networks Become Mainstream? China Accelerates 10G Optical Network Deployment as Global...
Qilin Ransomware Group Launches Massive "Korean Leak" Campaign Against Financial Sector Qilin Ransomware Group Launches Massive "Korean Leak" Campaign Against...
Can you retract an email that was sent by mistake? Can you retract an email that was sent by mistake?...
Steam Removes Malware-Infected Game That Stole $150000 in Cryptocurrency Steam Removes Malware-Infected Game That Stole $150000 in Cryptocurrency. Free game...
Could Quantum Computers Destroy Bitcoin? The Shor's Algorithm Threat Explained. Could Quantum Computers Destroy Bitcoin? The Shor's Algorithm Threat Explained....
Cyberattack Cripples Major European Airports-Forcing Manual Operations Cyberattack Cripples Major European Airports-Forcing Manual Operations Major European airports including London Heathrow,...