US Government Accelerates Post-Quantum Cryptography Transition as Quantum Threats Loom Closer
US Government Accelerates Post-Quantum Cryptography Transition as Quantum Threats Loom Closer
- Why Enterprise RAID Rebuilding Succeeds Where Consumer Arrays Fail?
- Linus Torvalds Rejects MMC Subsystem Updates for Linux 7.0: “Complete Garbage”
- The Man Who Maintained Sudo for 30 Years Now Struggles to Fund the Work That Powers Millions of Servers
- How Close Are Quantum Computers to Breaking RSA-2048?
- Why Windows 10 Users Are Flocking to Zorin OS 18 Instead of Linux Mint?
- How to Prevent Ransomware Infection Risks?
- What is the best alternative to Microsoft Office?
US Government Accelerates Post-Quantum Cryptography Transition as Quantum Threats Loom Closer
Federal agencies directed to procure only quantum-resistant products as new CISA guidance marks pivotal shift in cybersecurity strategy
January 30, 2026 — The United States government has taken a decisive step toward securing its digital infrastructure against future quantum computing threats, with the Cybersecurity and Infrastructure Security Agency (CISA) releasing comprehensive guidance that mandates federal procurement of quantum-resistant technology products.
The directive, issued pursuant to President Trump’s Executive Order 14306 signed last June, identifies specific categories of hardware and software that either currently support or are transitioning to post-quantum cryptography (PQC) standards.
The move signals an urgent shift from theoretical preparation to practical implementation as quantum computing advances accelerate faster than many experts previously anticipated.
The Quantum Clock Is Ticking
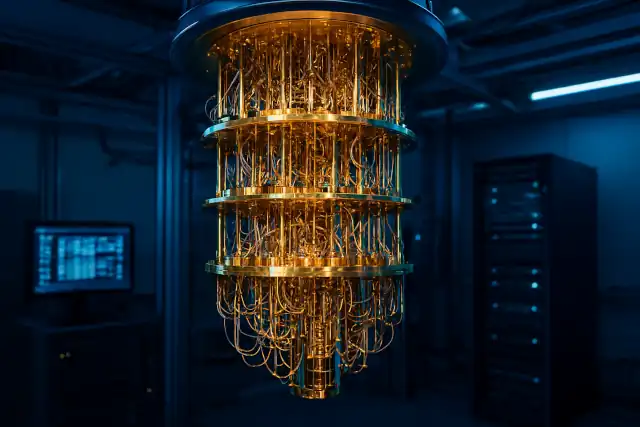
CISA’s guidance arrives at a critical juncture for cybersecurity. Recent breakthroughs in quantum computing have dramatically compressed the timeline for what experts call “Q-Day”—the moment when quantum computers become powerful enough to break today’s widely used public-key encryption systems.
New algorithmic improvements revealed in 2025 have reduced the hardware requirements for breaking encryption by approximately 95%. Where previous estimates suggested 20 million physical qubits would be needed, researchers now believe fewer than one million qubits could crack current encryption standards in less than a week. IBM’s quantum roadmap projects fault-tolerant systems with hundreds of logical qubits by 2029, while companies like IonQ have announced accelerated timelines targeting 80,000 logical qubits by 2030.
“The advent of quantum computing poses a real and urgent threat to the confidentiality, integrity and accessibility of sensitive data—especially systems that rely on public-key cryptography,” CISA stated in its announcement.
Mandated Technology Categories
The CISA guidance specifically targets IT products commonly procured by federal agencies that employ cryptographic algorithms for encryption or authentication.
The initial list encompasses:
- Cloud Services: Platform-as-a-Service (PaaS) and Infrastructure-as-a-Service (IaaS) offerings that have implemented or are implementing PQC standards
- Collaboration Software: Enterprise communication and teamwork platforms that handle encrypted data transmission
- Web Infrastructure: Both web browsers and servers that must secure online communications
- Endpoint Security: Full-disk encryption and data-at-rest encryption solutions that protect stored information
- Networking Hardware and Software: Equipment and applications managing secure network communications
- The directive is unambiguous: when a product category appears on CISA’s list as having widely available PQC capabilities, federal agencies must procure only quantum-resistant products within that category. The agency has committed to regular updates as quantum-resistant technologies evolve.
Global Standards Provide Foundation
The urgency driving CISA’s directive builds upon foundations laid by the National Institute of Standards and Technology (NIST), which finalized its first three post-quantum cryptography standards in August 2024. These Federal Information Processing Standards specify quantum-resistant algorithms:
- ML-KEM (Module-Lattice-Based Key-Encapsulation Mechanism), derived from CRYSTALS-Kyber, serves as the primary standard for general encryption with notably small encryption keys and fast operation speeds.
- ML-DSA (Module-Lattice-Based Digital Signature Algorithm), based on CRYSTALS-Dilithium, handles general-purpose digital signature protocols.
- SLH-DSA (Stateless Hash-Based Digital Signature Standard), evolved from SPHINCS+, provides an alternative hash-based signature approach.
In March 2025, NIST selected a fourth algorithm, Hamming Quasi-Cyclic (HQC), as a backup for ML-KEM. This code-based scheme uses different mathematical foundations than the lattice-based ML-KEM, providing crucial redundancy should vulnerabilities emerge in the primary standard. NIST expects to release the draft HQC standard in early 2026, with finalization in 2027.
Two of these standards were developed by IBM Research cryptographers, marking a significant contribution from private sector innovation to national security infrastructure.
The Industry Race Against Quantum Threats
The private sector is responding to quantum threats with unprecedented urgency and investment. Quantum computing companies raised $3.77 billion in equity funding during the first nine months of 2025—nearly triple the $1.3 billion raised in all of 2024. National governments invested $10 billion in quantum technologies by April 2025, up from $1.8 billion throughout 2024.
Major technology providers are already integrating PQC into their offerings:
- Cloudflare achieved a milestone in late October 2025 when the majority of human-initiated traffic to its network became protected by post-quantum encryption—validating that widespread deployment is technically feasible.
- IBM unveiled its Quantum Nighthawk processor with 120 qubits and advanced connectivity in November 2025, alongside demonstrations of all key components needed for fault-tolerant quantum computing.
- Google announced its Willow quantum processor, achieving below-threshold error correction—a critical milestone that halved error rates when scaling from 9 to 49 encoded qubits.
- Microsoft introduced its Majorana 1 topological qubit processor in February 2025, designed to scale to one million qubits using hardware-protected qubits.
These advances underscore why preparation cannot wait. As quantum hardware improves, the window for securing vulnerable data narrows.
The “Harvest Now, Decrypt Later” Threat
Security experts emphasize that the quantum threat is not merely future-oriented. Adversaries are likely already collecting encrypted data with plans to decrypt it once sufficiently powerful quantum computers become available—a strategy known as “harvest now, decrypt later.”
This reality makes immediate action imperative for any organization handling sensitive information with long-term confidentiality requirements. Data that must remain secure beyond 2035 needs quantum-resistant protection today.
“Any data you want to keep confidential beyond 2035 needs protection now,” warned cybersecurity researchers tracking quantum decryption timelines.
International Coordination and Compliance Deadlines
The United States is far from alone in recognizing quantum threats. International coordination is accelerating:
- Malaysia unveiled its National Post-Quantum Cryptography Readiness Roadmap in October 2025, positioning itself as a leader in Southeast Asian quantum preparedness.
- The European Union published its roadmap with compliance deadlines set for 2030 and 2035 depending on application criticality.
- The United Kingdom matched the common 2035 deadline for full national migration to quantum-resistant systems.
- Australia set an aggressive 2030 deadline for migration to PQC.
The U.S. government’s own timelines, established through National Security Memorandum 10 and reinforced by the Quantum Cybersecurity Preparedness Act, target 2035 for comprehensive migration. The Commercial National Security Algorithm Suite 2.0 (CNSA 2.0) establishes intermediate milestones, requiring all new National Security Systems acquisitions to be CNSA 2.0 compliant by January 1, 2027, with final mandatory compliance for most systems by 2033.
Technical Challenges and Market Growth
The transition to post-quantum cryptography presents significant technical and organizational challenges. Many organizations lack comprehensive quantum risk readiness, with surveys indicating approximately 48% of firms have not taken preparatory actions despite the looming threat.
Migration timelines can extend over a decade due to complex legacy infrastructure, embedded systems in operational technology, and Internet of Things devices that may lack upgrade paths. The National Cybersecurity Center of Excellence is demonstrating practices to reduce deployment time through cryptographic discovery tools and migration frameworks.
Despite these challenges, the post-quantum cryptography market is experiencing explosive growth. Market analysis projects expansion from $420 million in 2025 to $2.84 billion by 2030, representing a compound annual growth rate exceeding 47%. Some forecasts suggest even faster growth, potentially reaching $5.3 billion by 2029.
Quantum-Safe Hardware and Hybrid Approaches
The transition strategy increasingly emphasizes quantum-safe hardware—embedding quantum-resistant encryption directly into devices rather than relying solely on software implementations. This approach encompasses specialized hardware modules and processors executing NIST-endorsed algorithms, enhancing both cryptographic functionality and processing speed.
Leading organizations advocate for hybrid cryptographic approaches that combine classical and post-quantum schemes. This strategy provides robust security during the transition period, ensuring protection even if vulnerabilities emerge in one component. The Federal Information Processing Standards now permit validation of hybrid algorithms under FIPS 140-3 compliance frameworks, facilitating gradual integration while maintaining compatibility with existing systems.
Expert Perspectives on Timeline Uncertainty
While quantum computing advances have been remarkable, experts caution against both complacency and panic. Timeline predictions for truly disruptive quantum computers vary widely—from five years to several decades, depending on whom you ask.
“I would say the jury’s still out,” noted Bill Fefferman, a quantum computing researcher, regarding whether quantum computers will deliver practical value within current researchers’ lifetimes. Even Google, while announcing breakthroughs, acknowledges in its own materials that “a useful, large-scale, error-corrected quantum computer that solves lots of practical, real-world problems is still a ways off.”
However, this uncertainty cuts both ways. The possibility of unexpected algorithmic breakthroughs or engineering advances means that waiting for certainty is not a viable strategy. Recent progress has already defied some pessimistic predictions—when Microsoft’s CEO stated in January 2025 that quantum computing remained 15 to 30 years from practical utility, the industry spent the year attempting to prove him wrong with tangible demonstrations of quantum advantage.
Recommendations for Organizations
CISA emphasizes that organizations should not limit quantum-safe preparations to products explicitly listed in the current guidance. The directive represents a starting point, not a comprehensive inventory. Organizations should:
- Conduct cryptographic inventories to identify where quantum-vulnerable algorithms are deployed across their infrastructure
- Prioritize high-value assets and long-term confidential data for early migration
- Engage with technology vendors about their PQC implementation roadmaps and timelines
- Monitor authoritative sources including NIST’s PQC website, CISA bulletins, and industry consortiums like the Quantum Economic Development Consortium
- Consider crypto-agility as a fundamental architectural principle, enabling rapid algorithm updates without extensive system redesigns
- Begin hybrid implementations where technically feasible to gain experience while maintaining backward compatibility
Looking Ahead: The Quantum-Safe Future
The release of CISA’s product category list represents more than bureaucratic guidance—it marks a inflection point in the global race to secure digital infrastructure against quantum threats. With clear government mandates, established international standards, and accelerating private sector implementation, the transition to post-quantum cryptography has moved from theoretical preparation to operational imperative.
The October 2025 Post-Quantum Cryptography Conference in Kuala Lumpur, which convened over 2,500 delegates from more than 30 countries, demonstrated the global scale of coordination required. The PKI Consortium’s introduction of the Post-Quantum Cryptography Maturity Model provides organizations with practical frameworks for assessing and advancing their quantum readiness.
As Cloudflare’s milestone demonstrates—with the majority of its traffic now post-quantum protected—widespread deployment is achievable with today’s technology. The question is no longer whether organizations will migrate to quantum-resistant cryptography, but how quickly they can complete the transition before quantum computers mature.
For federal agencies, CISA’s guidance provides both clarity and urgency. For private organizations, it serves as a clear signal that the era of quantum-safe computing has begun. The quantum future, once theoretical, is now a present-day procurement requirement and a fundamental element of cybersecurity planning.
The clock is ticking, but the tools for protection are available. The challenge now lies in implementation before the quantum advantage arrives.
For more information on post-quantum cryptography standards and migration guidance, organizations can consult: