Hackers Pose as WordPress Officials and Send Malicious Patch Links to Website Owners
Hackers Pose as WordPress Officials and Send Malicious Patch Links to Website Owners
- 60% of MD5 Password Hashes Can Be Cracked in Under an Hour with a Single GPU
- Dirty Frag: Root Access on Every Major Linux Distribution — No Patch, No Warning
- Ubuntu 26.04 LTS (Resolute Raccoon): The Most Ambitious Ubuntu LTS in a Decade
- Proton Mail: Data Transferred to FBI Again!
- How Close Are Quantum Computers to Breaking RSA-2048?
- How to Prevent Ransomware Infection Risks?
- What is the best alternative to Microsoft Office?
Hackers Pose as WordPress Officials and Send Malicious Patch Links to Website Owners
On December 6th, security firm Wordfence recently discovered hackers impersonating WordPress officials, sending phishing emails to website owners.
The emails claimed to detect vulnerabilities on the websites, potentially allowing hackers to execute remote code.
The website owners were instructed to use the patch link attached to the email, labeled CVE-2023-45124, to “fix the website vulnerability.”
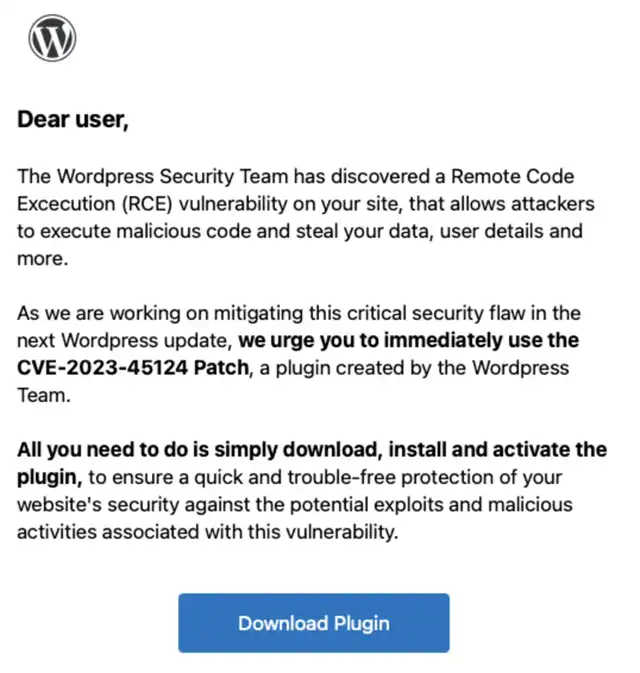
However, the link provided by the hackers actually directed users to a phishing website they had set up themselves. If victims did not verify the authenticity of the information and directly clicked on the web link, they would be directed to a counterfeit WordPress site, “en-gb-wordpress [.] org.”
According to official statements, once victims installed the purported “phishing patch,” it contained malicious software that added a hidden malicious admin account, wpsecuritypatch, in the website backend. The website URL and password were then sent back to the hacker’s server. Subsequently, a backdoor program, wpgate [.] zip, was implanted on the website, allowing hackers to maintain continuous control over the victim’s site.
It’s important to note that security researchers observed the hackers attempting to gain the trust of victims by adding multiple fake comments in the phishing site’s comment section. Additionally, they falsely listed some programmers from the security company Automattic as developers.


