Why Are Enterprises Adopting 3-2-1-1-0 for Data Safety?
Why Are Enterprises Adopting 3-2-1-1-0 for Data Safety?
- 60% of MD5 Password Hashes Can Be Cracked in Under an Hour with a Single GPU
- Dirty Frag: Root Access on Every Major Linux Distribution — No Patch, No Warning
- Ubuntu 26.04 LTS (Resolute Raccoon): The Most Ambitious Ubuntu LTS in a Decade
- Proton Mail: Data Transferred to FBI Again!
- How Close Are Quantum Computers to Breaking RSA-2048?
- How to Prevent Ransomware Infection Risks?
- What is the best alternative to Microsoft Office?
Why Are Enterprises Adopting 3-2-1-1-0 for Data Safety? The 3-2-1-1-0 Rule: A Modern Defense Against Ransomware
In an era where ransomware attacks have become one of the most significant threats to enterprise data security, organizations are evolving their backup strategies beyond traditional approaches.
The 3-2-1-1-0 rule has emerged as the gold standard for data protection, building upon the classic 3-2-1 backup strategy with additional safeguards specifically designed to combat modern cyber threats.
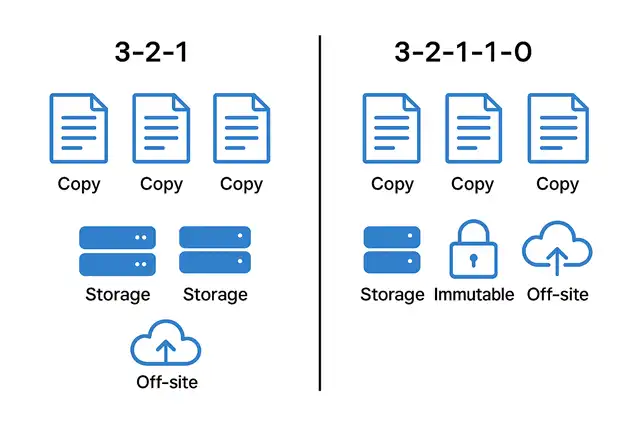
Understanding the 3-2-1-1-0 Rule
Let’s break down each component of this comprehensive backup strategy:
3 Copies of Your Data The foundation remains unchanged: maintain three separate copies of your critical data. This includes your primary production data plus two backup copies. Multiple copies provide redundancy—if one fails or becomes compromised, you have alternatives to restore from.
2 Different Media Types Store your backups on at least two different types of storage media. This might include disk-based storage, tape, cloud storage, or network-attached storage (NAS). Using different media types protects against vulnerabilities specific to a single technology. If a particular storage system has a flaw that ransomware exploits, your other backup remains safe.
1 Copy Offsite Keep at least one backup copy in a geographically separate location. This protects against physical disasters like fires, floods, earthquakes, or localized cyberattacks. For many organizations today, “offsite” means cloud storage, which offers geographic redundancy and accessibility.
1 Copy Offline (Air-Gapped) This is the critical addition that makes the strategy ransomware-resistant. An air-gapped backup is physically or logically disconnected from your network. Ransomware cannot encrypt what it cannot reach. This might be achieved through:
- Physical tape storage removed from tape libraries
- Immutable cloud storage with network isolation
- Removable drives that are disconnected after backup
- Network-isolated storage that’s only connected during backup windows
0 Errors in Backup Verification Regular testing and verification ensure your backups are actually restorable. Many organizations have discovered during ransomware incidents that their backups were corrupted, incomplete, or untested. Zero errors means:
- Automated backup verification processes
- Regular restoration tests
- Monitoring for backup job failures
- Validation of backup integrity and completeness
Why Ransomware Makes 3-2-1-1-0 Essential
Traditional backup strategies were designed primarily for hardware failures, human errors, and natural disasters. Ransomware fundamentally changed the threat landscape in several ways:
Ransomware Targets Backups Modern ransomware is sophisticated. Attackers often spend weeks inside networks before deploying encryption, specifically searching for and destroying backup systems. They know that without backups, victims are more likely to pay ransoms. Connected backup systems are prime targets.
Lateral Movement Threatens Connected Systems Once inside a network, ransomware can spread laterally to any connected system, including backup infrastructure. Network-attached backup storage, even if dedicated, remains vulnerable if attackers can access it through network credentials or vulnerabilities.
Speed of Encryption Ransomware can encrypt vast amounts of data in hours or minutes. If your only backups are on continuously connected systems, they can be encrypted before you even detect the attack. An air-gapped copy provides a guaranteed recovery point that attackers cannot touch.
Data Exfiltration and Double Extortion Many ransomware groups now steal data before encrypting it, threatening to release sensitive information unless paid. While this doesn’t directly affect backup strategy, having reliable recovery capabilities removes the encryption leverage, forcing organizations to only contend with the data leak threat.
Real-World Implementation Considerations
Implementing 3-2-1-1-0 requires balancing security with operational efficiency:
Automation is Critical The complexity of maintaining multiple backup copies across different media and locations makes automation essential. Manual processes are error-prone and don’t scale. Modern backup solutions can orchestrate the entire 3-2-1-1-0 workflow automatically.
Recovery Time Objectives Matter While air-gapped backups provide maximum security, they may be slower to restore from. Organizations typically use faster, online backups for quick recovery from minor incidents, reserving air-gapped copies for catastrophic scenarios like ransomware.
Cloud Storage as a Force Multiplier Cloud platforms excel at implementing several aspects of 3-2-1-1-0 simultaneously. Features like immutable storage, geographic replication, and logical air-gapping through access controls make cloud an attractive component of modern backup strategies.
Testing is Non-Negotiable The “0 errors” component requires discipline. Organizations should conduct regular disaster recovery drills that include restoring from air-gapped backups. These tests validate both technical capabilities and staff readiness.
The Cost of Not Implementing 3-2-1-1-0
The consequences of inadequate backup strategies are severe. Organizations hit by ransomware without air-gapped backups face impossible choices: pay substantial ransoms with no guarantee of data recovery, attempt to rebuild systems from scratch, or potentially go out of business. The downtime alone can cost millions, not counting ransom payments, regulatory fines, reputation damage, and lost customer trust.
In contrast, the investment in a robust 3-2-1-1-0 strategy—including additional storage, cloud services, and backup management tools—is modest compared to the potential losses from a successful ransomware attack.
Conclusion
The 3-2-1-1-0 backup rule represents the evolution of data protection for the modern threat landscape. It acknowledges that cyber attackers are sophisticated, persistent, and specifically targeting backup infrastructure. By maintaining multiple copies across different media, with at least one copy truly isolated from networks and all backups regularly verified, enterprises can ensure business continuity even when—not if—they face a ransomware attack.
For any organization handling critical data, 3-2-1-1-0 isn’t just a best practice—it’s a fundamental requirement for survival in today’s threat environment. The question is no longer whether to implement it, but how quickly you can achieve full compliance with all five components of this essential framework.
Major Fire at South Korean Government Data Center Destroys Seven Years of Critical Files


