Understanding End-to-End Encryption (E2EE): Applications and Use Cases
Understanding End-to-End Encryption (E2EE): Applications and Use Cases
- 60% of MD5 Password Hashes Can Be Cracked in Under an Hour with a Single GPU
- Dirty Frag: Root Access on Every Major Linux Distribution — No Patch, No Warning
- Ubuntu 26.04 LTS (Resolute Raccoon): The Most Ambitious Ubuntu LTS in a Decade
- Proton Mail: Data Transferred to FBI Again!
- How Close Are Quantum Computers to Breaking RSA-2048?
- How to Prevent Ransomware Infection Risks?
- What is the best alternative to Microsoft Office?
Understanding End-to-End Encryption (E2EE): Applications and Use Cases
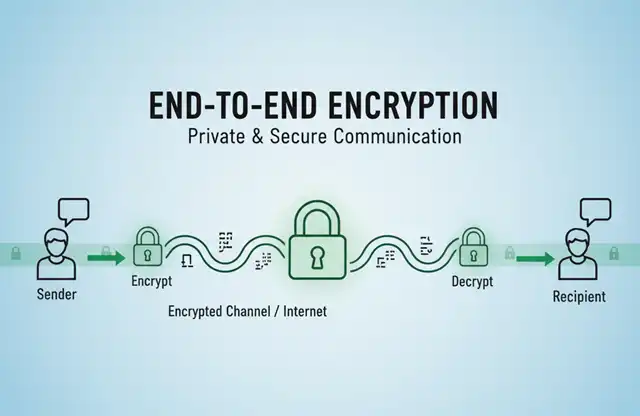
What is End-to-End Encryption?
End-to-end encryption (E2EE) is a security method that ensures only the sender and intended recipient can read the content of a communication.
In this system, data is encrypted on the sender’s device and can only be decrypted by the recipient’s device. No intermediary—including service providers, internet service providers, or even the platform hosting the communication—can access the unencrypted content.
The core principle of E2EE is simple yet powerful: encryption keys are generated and stored exclusively on users’ devices.
When you send a message, it’s encrypted before leaving your device, travels through networks as encrypted data, and is only decrypted when it reaches the recipient’s device.
This creates a secure “tunnel” between communicating parties, making interception or surveillance virtually impossible without access to the end devices themselves.
Applications Beyond Email
While E2EE is increasingly used in secure email services, its applications extend far beyond email communication:
1. Instant Messaging
Messaging apps represent the most widespread use of E2EE today. These platforms protect billions of daily conversations from unauthorized access.
Popular Apps:
- WhatsApp: Uses the Signal Protocol to encrypt all messages, calls, photos, and videos
- Signal: Considered the gold standard for encrypted messaging, offering complete E2EE for all communications
- Telegram (Secret Chats): Offers optional E2EE through its Secret Chats feature
- iMessage: Apple’s messaging service provides E2EE for messages between Apple devices
- Facebook Messenger (Secret Conversations): Offers optional E2EE mode
- Threema: Privacy-focused messenger with E2EE by default
2. Voice and Video Calls
E2EE protects real-time audio and video communications from eavesdropping.
Applications:
- FaceTime: Apple’s video calling service uses E2EE
- WhatsApp Calls: Both voice and video calls are end-to-end encrypted
- Signal Calls: Offers encrypted voice and video calling
- Wire: Professional communication platform with encrypted calls
- Zoom: Offers E2EE for meetings (requires enabling)
3. Cloud Storage and File Sharing
E2EE ensures that files stored in the cloud remain private, even from the service provider.
Services:
- Tresorit: Zero-knowledge cloud storage with E2EE
- Sync.com: Cloud storage with automatic E2EE
- ProtonDrive: Encrypted cloud storage from the makers of ProtonMail
- Cryptomator: Open-source tool that adds E2EE to existing cloud storage services
- SpiderOak: Backup and sync service with E2EE
4. Password Managers
These apps use E2EE to protect your most sensitive information—your passwords.
Apps:
- 1Password: E2EE password manager with zero-knowledge architecture
- Bitwarden: Open-source password manager with E2EE
- LastPass: Password manager with E2EE
- Dashlane: Offers E2EE for password storage and sharing
5. Note-Taking and Productivity
Secure note-taking apps protect sensitive information like financial data, personal thoughts, and business ideas.
Applications:
- Standard Notes: E2EE note-taking app
- Joplin: Open-source note app with E2EE synchronization
- Cryptee: Encrypted photo storage and document editor
- Notesnook: Privacy-focused note-taking with E2EE
6. Collaboration Tools
Business communication platforms increasingly offer E2EE for corporate security.
Platforms:
- Wire: Team collaboration with E2EE messaging and calls
- Wickr: Secure collaboration platform designed for enterprises
- Element (Matrix protocol): Decentralized communication with E2EE
7. Financial and Payment Apps
Some cryptocurrency wallets and financial apps use E2EE to protect transaction data.
Examples:
- Various cryptocurrency wallets with encrypted backups
- Secure payment messaging systems
- Banking apps with encrypted communication channels
8. Healthcare Applications
Medical apps use E2EE to comply with privacy regulations and protect patient data.
Use Cases:
- Telemedicine platforms
- Patient-doctor messaging systems
- Health record storage apps
Why E2EE Matters
End-to-end encryption has become essential in our digital age for several reasons:
- Privacy Protection: Safeguards personal conversations from surveillance
- Data Security: Protects sensitive information from hackers and data breaches
- Trust: Users maintain control over their data without relying on service providers
- Compliance: Helps organizations meet regulatory requirements like GDPR and HIPAA
Conclusion
End-to-end encryption has evolved from a niche security feature to a fundamental expectation in digital communication. Its applications now span messaging, voice calls, file storage, productivity tools, and beyond.
As privacy concerns grow and cyber threats become more sophisticated, E2EE continues to be an essential technology for protecting our digital lives.
When choosing apps and services, looking for true end-to-end encryption is one of the most important steps you can take to secure your personal information.
Why Proton Mail Offers Superior Security and Privacy Compared to Gmail
The best free email with end-to-end encryption (E2EE)
End-to-End Encryption in VoIP: Understanding SIP Protocol and E2EE Support


