Will Quantum Computers Break All Our Passwords in 20 Years?
Will Quantum Computers Break All Our Passwords in 20 Years?
- 60% of MD5 Password Hashes Can Be Cracked in Under an Hour with a Single GPU
- Dirty Frag: Root Access on Every Major Linux Distribution — No Patch, No Warning
- Ubuntu 26.04 LTS (Resolute Raccoon): The Most Ambitious Ubuntu LTS in a Decade
- Proton Mail: Data Transferred to FBI Again!
- How Close Are Quantum Computers to Breaking RSA-2048?
- How to Prevent Ransomware Infection Risks?
- What is the best alternative to Microsoft Office?
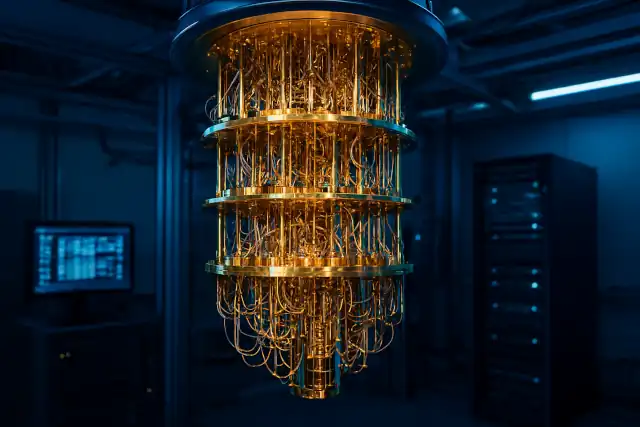
Will Quantum Computers Break All Our Passwords in 20 Years?
“Safe Today, But What About in 20 Years?” — The Quiet Global Push to Prepare for When Quantum Computers Break Encryption
The impact of quantum computers extends far beyond raw computing speed.
From classified government communications to our everyday online transactions, the encryption systems that underpin modern society are facing a fundamental reckoning due to advances in quantum technology.
What we need to understand now is that quantum represents both a threat and an opportunity to strengthen our defenses.
This article explores the relationship between quantum computing and cryptography based on insights from his work.
How Close Are Quantum Computers to Breaking RSA-2048?
When Encryption Can Be Broken
One catalyst for the surge of interest in quantum computers was mathematician Peter Shor‘s 1994 discovery of a factorization algorithm.
Shor proved that quantum computers, operating on fundamentally different principles than conventional machines, could efficiently solve prime factorization and related mathematical problems.
In practical terms, this means that with a fully functional quantum computer, problems like prime factorization become trivial—and cryptographic systems like RSA encryption and the elliptic curve cryptography used in Bitcoin signatures could be compromised.
Could Quantum Computers Destroy Bitcoin? The Shor’s Algorithm Threat Explained
Just Because We Can’t Do It Now Doesn’t Mean We’re Safe
Of course, current quantum computers haven’t yet reached the scale needed to break these encryption schemes. However, simply waiting for quantum computing to mature before taking action would be too late.
Imagine a scenario twenty years from now where quantum computers have advanced enough to crack today’s encryption. At that point, even communications between governments from twenty years earlier—right now—could be decrypted and exposed. This isn’t merely theoretical: adversaries are already employing “harvest now, decrypt later” tactics, intercepting and storing encrypted data with the intention of decrypting it once quantum capabilities become available.
That’s why it’s crucial to adopt encryption methods now that can withstand future quantum computing capabilities.
China Telecom Achieves 100km Quantum Transmission Record
The Global Push for Post-Quantum Cryptography
To address this challenge, efforts led by the National Institute of Standards and Technology (NIST) have been underway in recent years to standardize “post-quantum cryptography” (PQC)—encryption algorithms designed to resist even quantum computer attacks.
In August 2024, NIST released its first finalized Post-Quantum Cryptography standards, including quantum-resistant algorithms like CRYSTALS-Kyber, CRYSTALS-Dilithium, and SPHINCS+. Following this announcement, major American technology companies including Google and NVIDIA have launched collaborative initiatives to implement post-quantum encryption.
The knowledge gained from quantum information processing serves not only as a computational weapon but also as a shield—enhancing information security and improving data quality through solutions like post-quantum cryptography.
Will the quantum encryption become a joke after a 10-year-old desktop computer breaks it in 4 minutes?
The Quantum Threat Timeline
Recent assessments paint a sobering picture of the timeline. According to the Global Risk Institute’s 2024 report, there’s an estimated 17-34% probability that a cryptographically relevant quantum computer capable of breaking RSA 2048 encryption will exist by 2034, with that probability rising to 79% by 2044.
Meanwhile, quantum computing investment surged by nearly 50% in 2024, reaching approximately $2 billion, as advances in qubit stability and error correction signal a shift from simply scaling qubit counts toward building more practical, reliable systems.
Despite growing awareness of quantum threats, many organizations remain unprepared. Recent surveys reveal that 40% of organizations aren’t aware of their company’s quantum preparedness plans, and 41% currently have no plans to address quantum computing threats.
Quantum Computers Will Break Today’s Encryption And Hackers Are Already Preparing
What Is Quantum Cryptography?
Alongside post-quantum cryptography, development is also progressing on “quantum cryptography”—encryption that leverages quantum mechanical principles themselves.
Quantum cryptography offers exceptional resistance not only against quantum computer attacks but against any form of decryption attempt. It represents encryption that cannot be broken unless one violates the fundamental laws of quantum mechanics.
A prime example is “Quantum Key Distribution” (QKD), developed by Charles Bennett and Gilles Brassard in the 1980s. This system uses the characteristics of quantum mechanics to protect communication security.
Information is embedded in quantum superposition states, and if a third party attempts to eavesdrop, the act of observation disturbs the quantum state, leaving detectable traces of the intrusion. This makes unauthorized interception fundamentally detectable.
Why PQC Encryption Technology Can Resist Quantum Computing Decryption
The Race Against Time
The quantum computing revolution presents a paradox: the same technology that threatens to undermine our current security infrastructure also provides the tools to build stronger defenses. As we stand at this crossroads, the question isn’t whether quantum computers will break today’s encryption—it’s whether we’ll be ready when they do.
The message from cybersecurity experts and government agencies is clear: organizations cannot afford to wait for certainty before acting, as the migration to post-quantum cryptography will require years of coordination, testing, and infrastructure changes. The data we encrypt today may need protection for decades to come, making immediate action not just prudent, but essential.
As quantum computing transitions from laboratory curiosity to practical reality, the global race is on—not just to build more powerful quantum computers, but to ensure that when they arrive, our defenses are already in place.